In its last and final report, the Cyber Safety Review Board (CSRB) made a series of recommendations on how to improve the process for notifying and supporting victims of cyber attacks. Chief among these was a call for cloud service providers to work with device makers to deliver native notifications through mobile operating systems–a process similar to how AMBER Alerts and flood warnings are delivered today. While such an AMBER Alert system may not be viable in the short term, my new report out today seeks to outline what such a system might look like in the long term.
The problem that the CSRB recommendation is intended to address is all too real. Victims of cyber incidents are often difficult to reach and likely to dismiss an email or text message notifying them of a security incident as yet one more attempt by criminals to lure them into a scam or compromise their account.
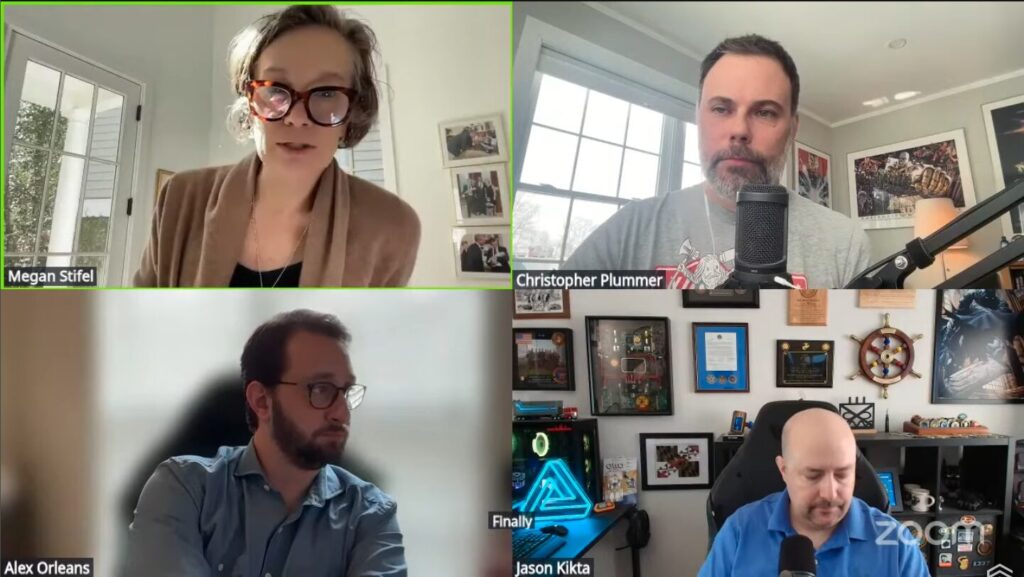
In my latest project with IST, I provide a roadmap for how to move the idea of AMBER Alerts for cyber victims from concept to reality. In Improving Private Sector Cyber Victim Notification and Support, I concretize the challenges and sketch out the design and governance of such a system.
While there is merit in the concept of an AMBER Alert system for improving cyber victim notification, getting mobile device makers and other stakeholders to commit to developing such a system will be a challenge. The carrots and sticks that have led to wide adoption of the actual AMBER Alert system are not readily available to compel development and deployment of a parallel system for cyber victim notification. Absent the legal framework and federal funding that has made the AMBER Alert system successful, at this time there is simply not the appetite among relevant stakeholders to build such a system on their own.
I conducted this research effort in collaboration with a working group of technical and policy experts. They resoundingly agreed that the challenges with cyber victim notification identified by the CSRB are real, but noted a lack of collective interest in developing such a system. To quote one participant, “this isn’t on my top fifty list of problems that need solving in cyberspace.” Another stated, “This is a problem for us. But not enough of one for us to invest in building this system.”
In the near term, the best course of action is for cloud service providers to commit to verifying and validating that notifications sent through existing channels are received, trusted, and acted upon. Given the (warranted) wariness of today’s Internet users, simply delivering a notification is not sufficient.
However, when faced with a high-impact, high-stakes cyber incident, a concerted effort in the form of emails, texts, and phone calls should be able to reach most victims and gain their trust. These communications may at first seem to originate from a very persistent scam operator, but eventually, the victim will likely take a moment to log in to a web portal and verify the message with a company they trust.
The investment required to build the native notification system envisioned by the CSRB for high-impact situations will only be justified if valid, verifiable, and trusted notifications can be delivered in a much broader set of circumstances.
At present, I do not anticipate that relevant stakeholders will move forward with the CSRB’s vision for native notification. However, in a few years and after a few more major cyber incidents, I would not rule out the possibility that investing to make the CSRB’s vision a reality may seem like a no-brainer. When that time comes, I hope this solutions-oriented report will serve as a useful tool for moving forward.