The international community has made steady progress in executing major disruptions through public-private cooperation, from the takedowns of Trickbot and Qakbot, to Operation Endgame, a multi-stage, coordinated campaign against cybercriminals. These disruptions have succeeded in part because they have effectively capitalized on information-sharing partnerships among public and private sector actors. Most cybersecurity practitioners, however, agree that more can be done to reach a greater level of impact from the disruptive activity. Since the launch of its initial recommendations in 2021, IST’s Ransomware Task Force has been working on developing stronger operational public-private sector partnerships to tackle these challenges. Last year, we hosted EXERCISE VEIL STORM I, a tabletop exercise focused on operational coordination across international law enforcement agencies and private sector firms in responding to cyber incidents. A recently-published Exercise Veil Storm I After Action Analysis summarizes the proceedings and findings of that exercise, which took place at the Europol Headquarters in The Hague on the margins of the 2024 Europol Cybercrime Conference.
And in continuation of our efforts to enable ransomware disruption, just last month we hosted EXERCISE VEIL STORM II, a follow-up tabletop exercise to the first. What exactly is a tabletop exercise? And how is IST supporting efforts to disrupt the ransomware ecosystem?
In this month’s edition of The TechnologIST, IST’s Sophia Mauro sat down with Director for Digital Security Taylor Grossman to learn more about her work on ransomware disruption and a recent tabletop exercise she helped to lead in The Hague.
1. What is the purpose of a tabletop exercise, or TTX? How are you leveraging TTXs in the ransomware disruption context?
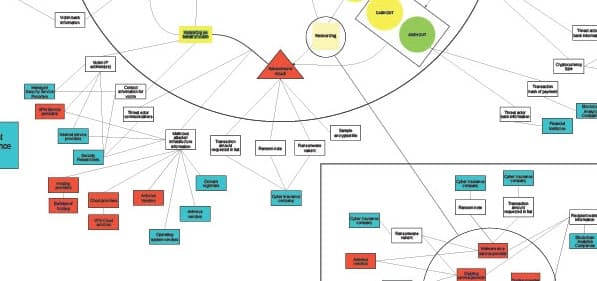
Taylor: “Table top exercises can serve a number of purposes – they can be used to simulate potential future scenarios, test response readiness, or generate exploratory discussions. Exercise VEIL STORM I was designed to walk through a hypothetical ransomware incident and explore response roles across diverse organizations, including the financial sector, threat intelligence, and law enforcement. We were focused on identifying what kinds of information are visible to which organizations: a blockchain analytics firm may be able to see active wallets, a financial institution may see victim banking information, while a threat intelligence firm may see victim IP addresses and attacker infrastructure, and so on. These unique vantage points in turn create information sharing opportunities that, when combined, could support the development of campaigns to cripple the ransomware ecosystem.
In our most recent TTX—called Exercise VEIL STORM II—we built off of the first TTX to develop an operational plan for a disruptive action. There was no set scenario; instead, after we presented an update on the evolving ecosystem of cybercrime enablers, organizations brainstormed ways to reduce cyber criminal activity by working together to target bad actors.”
2. How do you decide who to include in a tabletop exercise, and what else do you do to ensure that it is effective?
Taylor: “Our goal is to bridge communities and find ways to work together effectively. In both TTXs, we assembled organizations from across a broad spectrum of sectors, including participants from country cybersecurity centers; international and national law enforcement agencies; tech companies; financial institutions; blockchain analysis firms; and cyber threat intelligence providers. Finding the right size for a TTX can be difficult: ideally, organizers want to balance engaging diverse perspectives with building a trusted community. In our case, we recruited around 30 participants for both TTXs to strike the right balance for stimulating a good discussion. Importantly, we also maintained a Chatham House rule environment—meaning what’s said in the meeting can’t be attributed to a certain person or organization—that helped attendees feel more comfortable sharing sensitive observations and ideas.”
3. What does a TTX scenario look like? Can you give us an example of some of the questions that you might ask?
Taylor: “In Exercise VEIL STORM I, we led participants through a structured scenario of a fictional ransomware incident. We presented attendees with an invented ransomware group, “MantiCORE,” that had targeted three fabricated companies, each incorporated in different countries with different governance structures. The facilitators asked participants to react to developments in the attack and to propose response measures that their individual organizations might take to help remediate the situation. We asked questions like, “How would law enforcement respond to these incidents? What kind of barriers would inhibit real-time collaboration, and how could we address them?”
In Exercise VEIL STORM II, we took a slightly different approach: we asked participants much more open-ended questions about ideal disruption efforts they would like to see and about how their organization could contribute to those actions. Organizers purposefully encouraged broader, less structured conversations to try and solicit creative ideas. In the second half of the exercise, we then focused specifically on real world barriers to the proposed disruption efforts, and zoomed in on a few key steps that could be taken to move operational collaboration forward.”
4. What’s next for IST’s work on ransomware disruptions and offensive cyber operations?
Taylor: “We plan to take the ideas from last month’s TTX and put together an after-action report that proposes concrete steps forward. For example, how should organizations improve coordinated identification of top cybercriminal threats? Can the broader community draw on intelligence from more diverse communities, such as the gaming sector or insurance industry? We intend to distill these proposals into a tactical plan of action.
On a broader level, we at the Institute for Security and Technology continue to look at how to disrupt ransomware and cyber crime, including through our engagement with the International Counter Ransomware Initiative, our research into key case studies of past disruptions and the broader payment ecosystem, and our ongoing development of a framework for understanding acceptable private sector actions to reduce the threat of cybercrime.”