Since the inception of IST’s Ransomware Task Force in 2021, we have relied upon data to help underpin our understanding of trends in the ransomware ecosystem in order to support policy recommendations and facilitate meaningful action. This data helps us, along with security professionals, law enforcement, and governments, to assess trends. With the data, we can collectively build an understanding of the quantity of organizations and entities targeted, types and scale of compromised data, sectors that are most at risk, and common attack vectors.
As we mark the third year of the Ransomware Task Force, we continue our efforts to map ransomware incidents worldwide. This year, we focus our efforts on understanding the forces driving changes in victimology and on tracking new trends in previously under-reported geographic areas.
In the 2021 Combating Ransomware RTF report, we sought to paint a picture of the scope and scale of ransomware worldwide, relying on data from Recorded Future, Palo Alto’s Unit 42, Cloudian, Scitum, and Black Fog to map 2020/21 confirmed ransomware incidents. In the first edition of our global ransomware incident map, confirmed incidents skewed overwhelmingly towards the Global North. The United States, Canada, the United Kingdom, Australia, and Germany had the most confirmed incidents, with Brazil and India not far behind. Ransomware targets organizations and governments globally; tackling it in turn necessitates a global approach. As we wrote in the report, “Reducing the ransomware threat will require global cooperation due to the highly decentralized nature of cryptocurrency, dispersed nature of the criminal networks involved, the Internet’s basic infrastructure, and the differing legal and regulatory regimes around the world.”
Last year in 2022, we continued our efforts to map ransomware incidents worldwide with a retrospective analysis of incidents for the whole of calendar year 2021. RTF member Bob Rudis compiled data from Allan Liska at Recorded Future, Palo Alto’s Unit 42, Cloudian, Black Fog, and ecrime.ch to observe that nearly 70% of ransomware incidents impacted organizations with under 500 employees. That report also underscored the global reach of the ransomware threat, with attacks spanning almost all geographic boundaries and sectors.
This year, we turned to ecrime.ch, which aggregates messages posted on ransomware data leak sites (DLS), as the primary source of data. Data compiled by ecrime.ch provides an important snapshot of the total ransomware activity worldwide; however, it is biased towards ransomware attacks that use a traditional double-extortion approach.
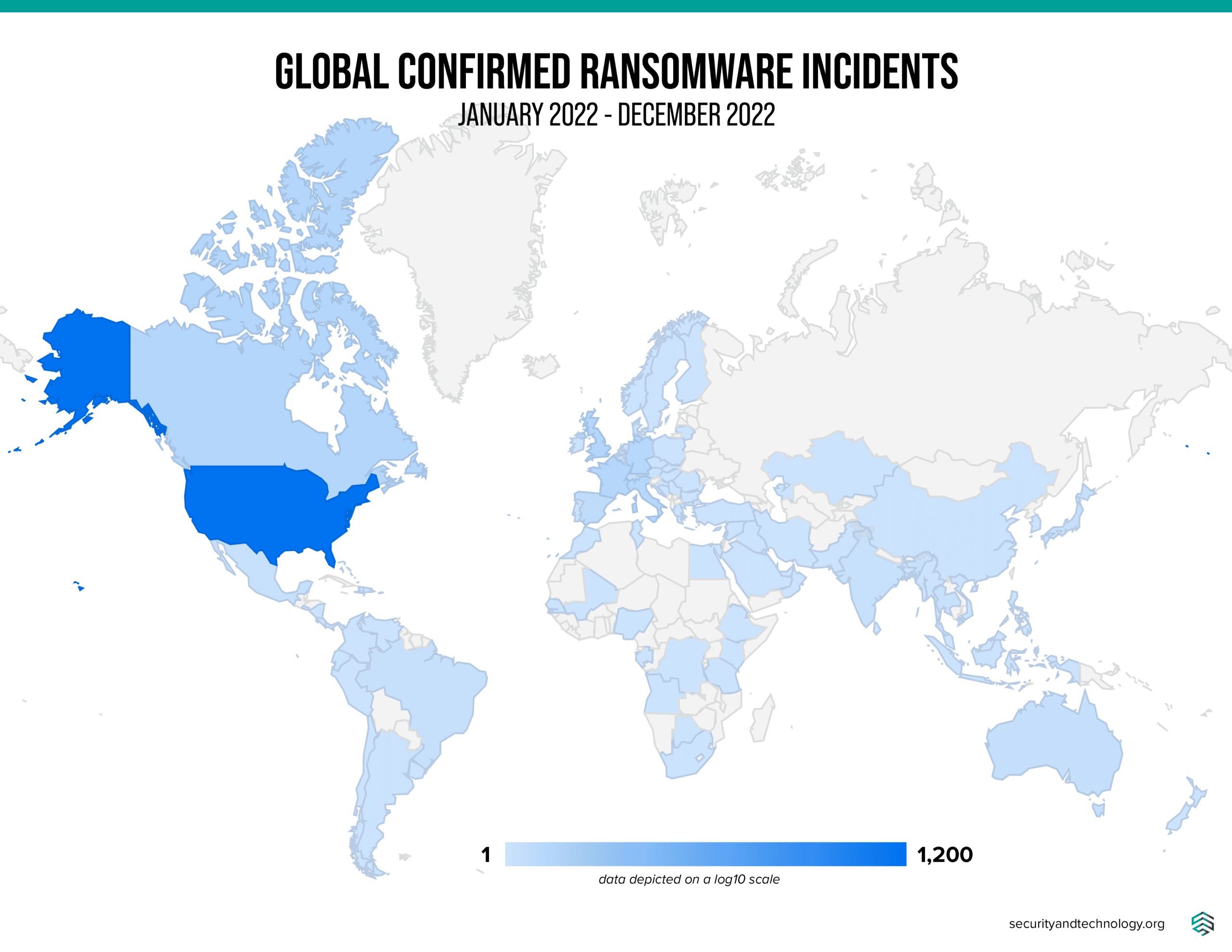
In calendar year 2022, we observed 2,600 ransomware incidents. Over the same period in 2021, per last year’s map of 2021 global ransomware incidents, we observed 3,000 incidents, suggesting a year-over-year decline in ransomware incidents. While these numbers reflect the available data, we note that the actual number of attacks is likely higher. This finding is consistent with the findings of other research institutions throughout 2022. While it is unlikely that a single force is driving this decline, the Russian invasion of Ukraine, law enforcement action, and continued efforts within the security community have almost certainly been contributing factors in this decline. Yet, early indications are that ransomware incidents in 2023 will reverse this decline.
According to ecrime.ch data, confirmed ransomware incidents occurred in 105 countries, originating from 58 ransomware groups. This number is relatively consistent with last year’s data, in which we calculated that incidents impacted organizations in 109 countries and documented at least 60 distinct ransomware families.
Though the overall statistics remain relatively consistent from last year to this year, there is more to the story: new trends in the ecosystem include the shifting dynamics of ransomware groups, the rise of the education sector as a key target, and the trends in geographic distribution of attacks.
Shifts in Ransomware Groups
In 2022, following public statements in support of Russia in the Russo-Ukrainian War, a Twitter user named @ContiLeaks leaked internal chat logs and tooling from the Conti ransomware group. Described as the “Panama Papers of Ransomware” by Trellix, this leak granted researchers and the public eye-opening insight into one of the most active ransomware groups of 2021-2022. By May 2022, the Conti group’s leak site went offline and several internal teams broke off to launch their own Ransomware as a Service (RaaS) offerings.
In an August 2022 post, the late Vitali Kremez describes how, following the disbanding of Conti, members formed new ransomware groups or shifted to other groups, including Royal (Zeon), BlackByte, Karakurt, BlackBasta, and Quantum. When we map ransomware attacks perpetrated by these groups along a timeline and outline the number of incidents linked to each of these groups, the overlaps begin to come into focus.

Ransomware groups Karakurt and BlackByte begin to appear on the timeline several months prior to the collapse of Conti and maintain a regular cadence of attacks from late 2021 through 2022. Establishment of these groups prior to the collapse of Conti indicates that they were likely created organically, rather than in response to the leak.
Following the exposure of Conti’s internal data at the start of March 2022, we observe a period of increased activity from the group through April and May, during which time they likely attempted to capitalize on remaining access to networks intended for ransom, before rebranding. In April 2022, BlackBasta launched their data leak site, and several months later Royal followed suit.
Global Initiative against Transnational Organized Crime’s Jack Meegan-Vickers describes fighting against ransomware groups as “a constant game of whack-a-mole.” Indeed, as long as the practice of ‘ransomware as a service’ remains profitable, when one group falls, another inevitably comes to take its place. But it remains important to understand the shifting dynamics of the groups involved in the ecosystem; identifying the group involved can indicate the types of methods employed, the type and composition of targets, and illuminate ways to ultimately mitigate the threat.
Rising Attacks Against the Education Sector
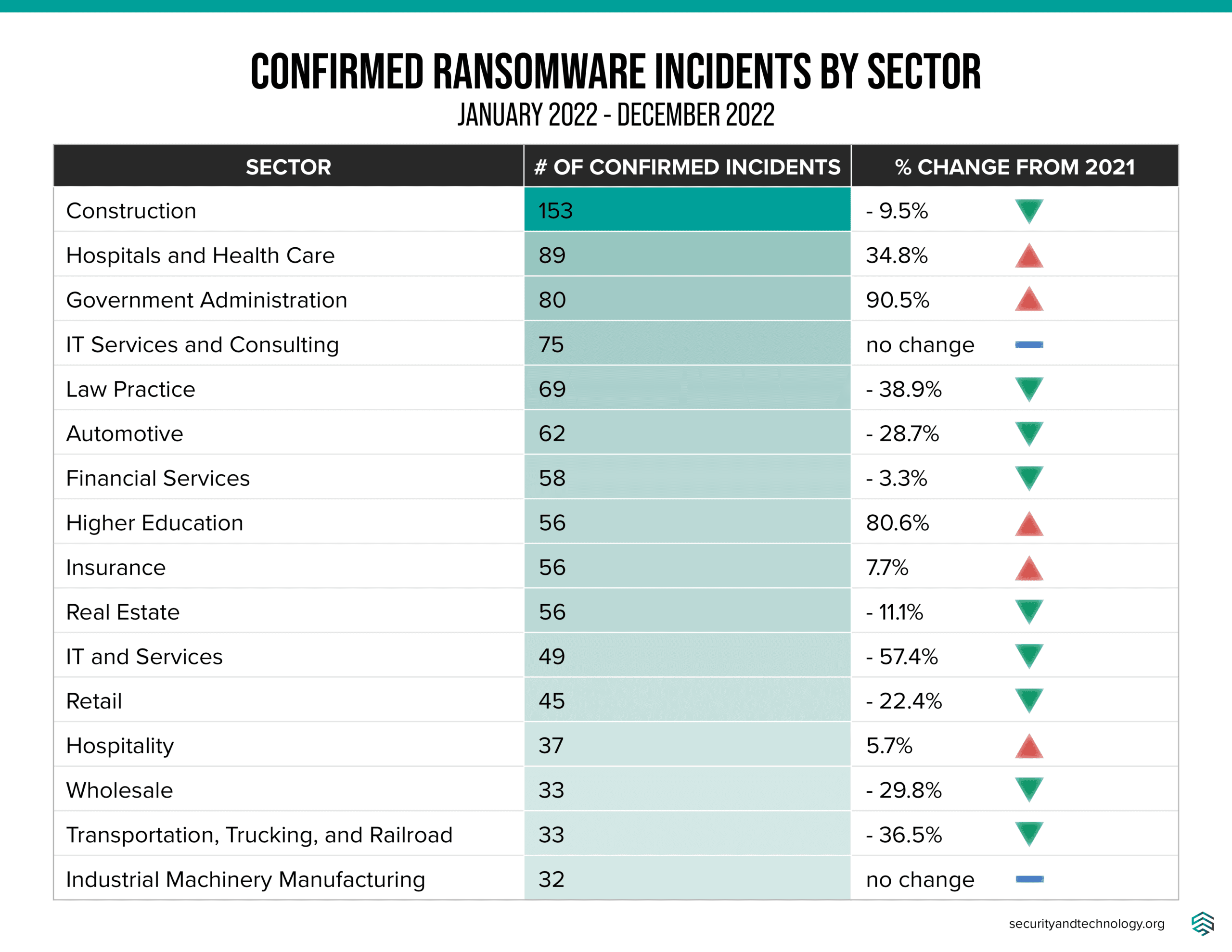
While the geographic distribution and size of organizations targeted by ransomware actors remained consistent across 2021 and 2022, the education sector saw an 80% increase in attacks from the previous year, a trend confirmed by ransomware researcher Allan Liska, who spotted it earlier this year.

The above chart maps confirmed instances of attacks on schools, universities, and other organizations in the education sector from January 2021 to September 2023. It depicts a steady increase in overall attacks, peaking at 32 attacks in June 2023. This upward trend throughout 2023 reflects, in large part, increased targeting by ransomware groups Vice Society and Rhysida, whose attacks have historically (though not exclusively) focused on education sector entities.
As we evaluated this timeline and began incorporating instances in which an impacted entity reportedly paid the ransom demand, we observed an uptick in attacks in the months following payment of a ransom demand. The below graph identifies two distinctive incidents targeting educational institutions in which the victim paid the ransom demand. While further study is needed to understand whether this trend is causal or merely correlated, the financial motivations of ransomware actors are likely to drive increased targeting against a sector following a payout in the hopes of achieving a similar outcome.

The Geography of Ransomware: Gaps and Trends
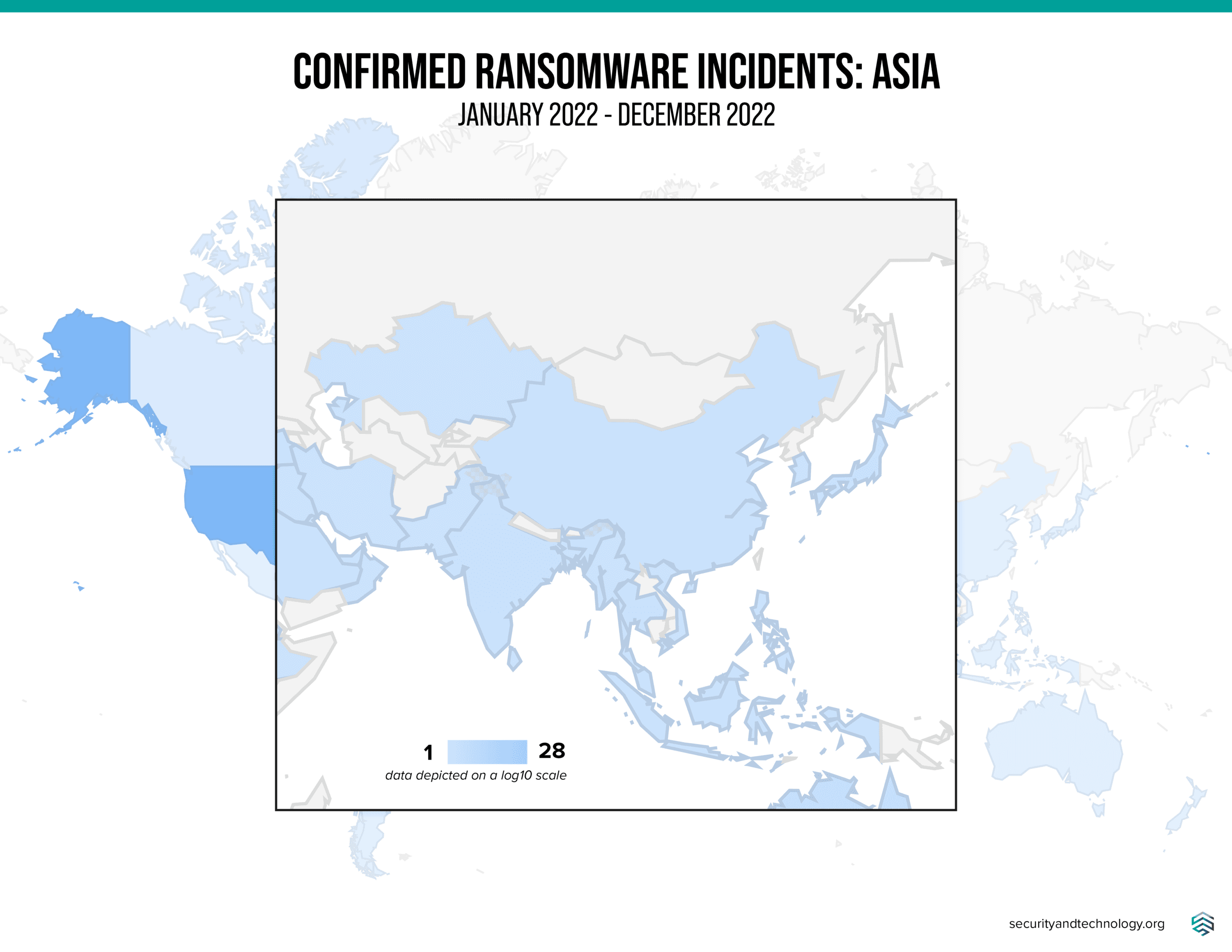
As acknowledged throughout the work of the Ransomware Task Force, from previous mapping efforts to the initial RTF Combating Ransomware report, ransomware is undoubtedly a global threat. While we continue to see large numbers of attacks reported in Europe and North America, we also want to be clear that this threat affects countries and economies across the globe. The data we have access to indicates that ransomware is a growing threat in nearly all emerging economies and throughout the Global South. By taking a look at some specific regions that are frequently under-researched or overlooked–especially by companies that are looking to feature research on specific markets based on projected profit margins–we can shine a light on the universal nature of the threat.
Notably, many of these under-researched countries have cybersecurity capacity constraints even more substantial than those faced by the countries in the Global North. Understanding the magnitude of the ransomware threats in distinct geographic regions will help governments, the technical community, and private sector actors better focus their scarce resources to counter this threat.
Africa
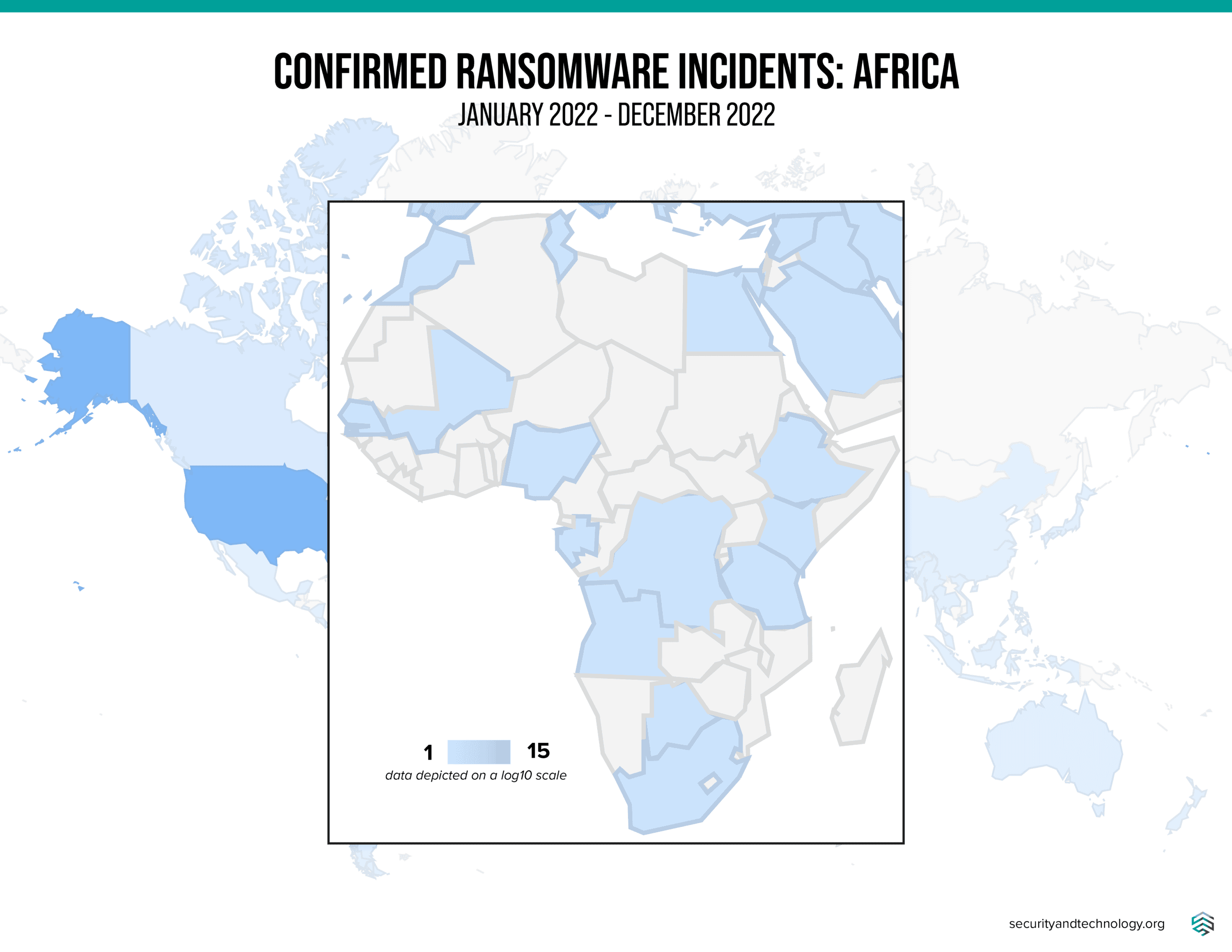
In 2022, ecrime.ch data identified 32 ransomware incidents against organizations in Africa that were reported on ransomware data leak sites, with the heaviest concentration of attacks against South Africa, Egypt, and Kenya.
The following four ransomware groups account for the majority of the observed attacks in Africa.
- LockBit
- PYSA
- Everest
- Conti
However, we believe that this data does not tell the full story: While findings from this data identify an overlapping set of ransomware groups, our discussions with regional counterparts have highlighted additional incidents of cyber extortion, carried out by threat actors operating within a small regional footprint who may not rely on public leak sites to extract a payment. Some of these incidents were not reflected within our own sample data, indicating that ransomware trends in Africa necessitate increased study to better understand the ransomware ecosystem beyond the largest international players.
A notable step towards expanding our collective understanding and building collaboration is the “Undermonitored Regions Working Group,” recently established by Tom Hegel from SentinelOne to better track espionage activity targeting Africa and Latin America. This type of collaboration will be essential to building up collective defenses against the threat of ransomware, whether in Africa, Latin America, or elsewhere. Going forward, we hope to see similar efforts focused on ransomware and other extortion-based attacks in under-served markets.
Republic of Singapore
Ransomware incident data for the Republic of Singapore highlights an important trend in attack methodology, as well as gaps between the number of incidents posted on public data leak sites and those confirmed internally. Ecrime.ch data only documented 13 attacks, while the Cyber Security Agency of Singapore identifies 132 reported cases involving ransomware in their Cyber Landscape 2022 report. This discrepancy between ecrime.ch data and official CSA estimates demonstrates the importance of incident reporting: public data leak sites can only go so far. A variety of scenarios, such as organizations that reported a breach, successfully prevented data encryption, paid the ransom demand to prevent data from being publicly leaked, or did not see their data posted publicly on a data leak site, could contribute to this difference in estimates.
The Singapore Cyber Landscape 2022 report also notes the increased rate of malware-free attacks, in which attackers breach an organization and extort victims by threatening to leak sensitive information. Unlike ransomware, which locks the data of victims until they pay the ransom demand, malware-free attacks leverage the threat of data exposure against organizations to drive them to pay a ransom demand, making it harder to track incidents. As this form of attack gains popularity, it is increasingly important for organizations to disclose incidents to private sector partners and report the breach through official government processes. These disclosures help researchers and law enforcement understand the scope and adoption rate of this method of cyber extortion. As ransomware actors continue to evolve their operations and develop new methods for conducting extortion-based attacks, understanding developing tradecraft requires support from impacted parties and partnerships with the private sector and governments in order to build effective methods of countering and disrupting future attacks.
Outlook
This year’s edition of the map, together with last year’s version, reveals overarching consistency in the countries and sectors impacted by ransomware attacks, demonstrating that the profile of organizations targeted has not changed. In sectors in which we have seen increased attacks, such as education, healthcare and government, ransomware actors have continued the trend of “following the money,” in which actors target entities who have either previously paid a ransom demand or seem capable of doing so.
Early numbers from calendar year 2023 show ransomware has clearly continued to impact organizations globally–something that we at IST and the Ransomware Task Force continue to track. The threat of ransomware shows no signs of abating, but as indicated by our May 2023 Progress Report, governments and the private sector have risen to meet this threat. As we continue to work towards reducing the volume and scale of ransomware attacks, the partnerships and collaborations we build become increasingly important in disrupting ransomware.




