The Trump Administration today released President Trump’s Cyber Strategy for America with six key priorities that “communicate the Trump Administration’s cyber vision approach to the American people, to Congress, to our partners in industry and allies across the globe–and also to adversaries.”
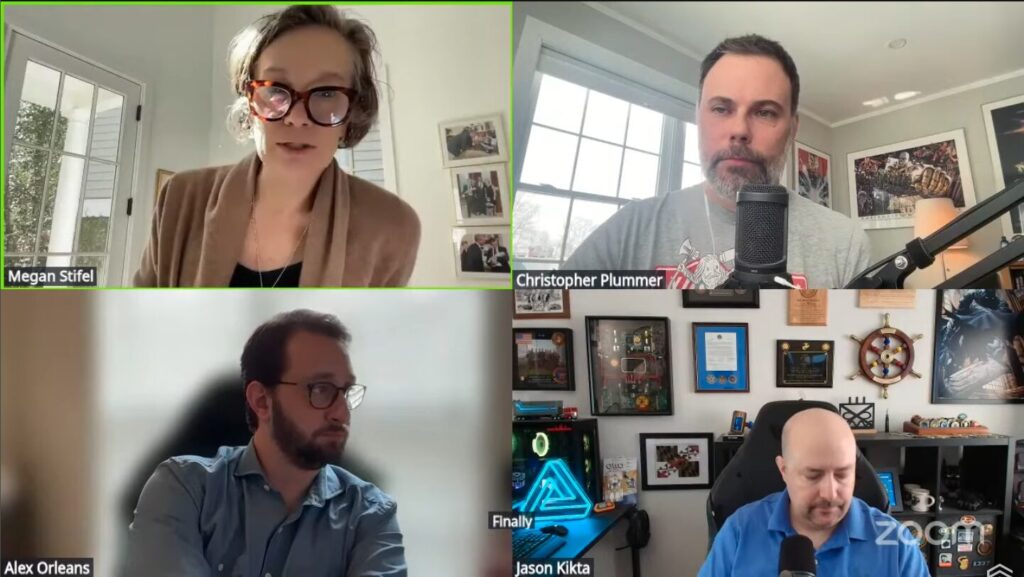
We asked experts from IST to weigh in on the strategy. In their quick takes, they commented on what’s there and what isn’t, where they see opportunities, and what it means for cybersecurity going forward.
Nicholas Leiserson:
“There’s not a lot to disagree with in the 2026 Cyber Strategy, but there’s also not a lot in it at all. The key points of emphasis, from protecting critical infrastructure and federal networks to disrupting adversaries, are similar to the 2023 iteration, which itself built on President Trump’s first strategy. I appreciate the continuity from past strategies, especially the emphasis on sensible cybersecurity regulation and building in security at the foundation of technology.
“However, without the backing of a comprehensive implementation plan, no strategy can meaningfully improve our cybersecurity posture. The Office of Management and Budget’s recent decision to roll back software supply chain security safeguards, even as threat actors increasingly target software vulnerabilities or actively insert them, is deeply concerning. What’s more, it is a significant threat to government cybersecurity, in opposition to the strategy’s focus on modernizing federal systems and streamlining regulations. I hope Director Cairncross will use the launch of the strategy to rein in agencies that are acting at cross purposes to its intent.”
Megan Stifel:
“At a high level, the six stated pillars of the 2026 Cyber Strategy closely resemble key focuses from prior strategies, including the first Trump administration and the Biden administration. I am grateful for that continuity, and for the fact that the administration stepped back from a more offensive-first approach that was in prior drafts. Disruption is a critical part of any comprehensive approach to cybersecurity, but it must be balanced against attention to the underlying incentive structure that allows software to be shipped to market rife with security flaws. It must also be balanced against attention to the known vulnerabilities and end-of-life devices that cyber criminals capitalize on to carry out attacks.”
“For years, the Ransomware Task Force has called for more government action to address the legal and policy frameworks that limit industry and government from collaborating at scale to take lawful measures against cyber criminals. I am hopeful that the administration’s intent to incentivize activities to identify and disrupt adversary networks will bear fruit, but it will only succeed if developed in close collaboration with industry and civil society leaders who have experience coordinating disruptions.”
Steven M. Kelly:
“Fueling and protecting American innovation is a core national security imperative, and I’m glad to see it prominently reflected in the new cyber strategy. Casting that imperative in the frame of advancing ‘global stability’ is notably new — and important. Emerging and disruptive technologies like AI and quantum computing can be engines of strategic surprise and lead to geopolitical instability. The United States and our allies must remain at the leading edge of innovation to ensure that, in the competition that matters most, the element of surprise works in our favor — not against us.”
Joshua Corman:
“When everything’s critical, nothing is. We’re most acutely concerned about threats to public safety and human life. UnDisruptable27 is eager to work with this White House and Executive Branch on ensuring ruthless prioritization for the fight that’s coming.
“I was glad to see the 2026 Cybersecurity Strategy list securing critical infrastructure as one of its six key pillars, particularly its callout of water utilities and hospitals as particularly at risk.
“It was, however, surprising to see no explicit mention of the Typhoons, especially given the urgency needed to address them, potentially as early as 2027. Regardless, resilience is about our ability to take a punch from any accident or adversary. Building our resilience–including through efforts like UnDisruptable27–can help to protect American lives.
No water, no hospitals, no kidding.”
Michael Klein:
“The 2026 Cyber Strategy includes critical infrastructure security, but falls short on the specific support that state, local, Tribal, and territorial (SLTT) governments–including K-12 schools–need to defend themselves against the transnational criminal organizations and adversaries that target them daily. Pillar 4 dedicates just one sentence to SLTT: “We will galvanize the role of state, local, Tribal, and territorial authorities as a complement to–not a substitute for–our national cybersecurity efforts.” This statement is correct in principle: we shouldn’t expect every town to stand up its own cyber-defense army to protect against nation-state adversaries. However, the strategy provides no roadmap for how the federal government will actually fulfill that cyber defense role and seems to stand at odds with the Administration’s actions to date. The State and Local Cybersecurity Grant Program, which provided critical funding for baseline protections, was not included in the President’s budget. The Multi-State Information Sharing and Analysis Center, which offered no-cost threat monitoring and services to all SLTT entities, has seen all federal funding removed.
“What the strategy does get right is the emphasis on moving away from “costly checklists” to meaningful security outcomes, and the recognition that private sector innovation must be paired with federal coordination. To operationalize the principles for K-12 schools specifically, the Administration should work with Congress on Universal Service Fund Reform. As IST outlined in our recent policy memo, the FCC’s cybersecurity pilot received $3.7 billion in requests against a $200 million budget, demonstrating demand for secure broadband is 18 times current capacity. If the Administration wanted to have a real impact on K-12 cybersecurity, the FCC could extend or expand the cybersecurity pilot program tomorrow.”
IST does not take institutional positions on public policy issues; the views represented herein are the author[s]’s own and do not necessarily reflect the views of IST.