The Institute for Security and Technology will once again join the global community of cyber experts in convening in San Francisco for the RSA Conference, March 23 – 26.
At IST, our mission is to unite policymakers, technology experts, and industry leaders to identify and translate discourse into impact. RSA is an annual opportunity for our team members and adjuncts to share our work, stay up to date on the latest technological and policy developments impacting cybersecurity, and look to the future. We’re eagerly anticipating connecting with you all!
Here’s where you can find the Institute for Security and Technology team, adjuncts, RTF Co-Chairs, and Steering Committee members at RSAC.
Monday
Supply Chain and Theory of Constraints in AI
Monday, March 23, 9:00 AM – 9:30 AM PDT | Moscone South 306
Joshua Corman, Executive in Residence for Public Safety & Security, Institute for Security and Technology & Founder, I Am The Cavalry
Alan Shimel, Founder, CEO, & Editor-in-Chief, Techstrong Group
Damon Edwards, Co-Founder & CEO, Attestify
Measuring Cyberspace-wide Success Against Threat Actors – [MASH2-M04]
Monday, March 23, 10:50 AM – 11:40 AM PDT | Moscone West 3007
Defenders are having more success against threat actors than we might fear. This session will reveal a new framework, packed with data and insights from the Cyber Threat Alliance and many others, sheds light not just on how each of us are succeeding against attackers, but how all of us are, as a community.
Michael Daniel, President and CEO, Cyber Threat Alliance, and RTF Co-chair
Jason Healey, Senior Research Scholar, Columbia University School of International and Public Affairs
Preparing for AI Vulnerability Exploitation: Preventing Cataclysm – [IAIS-M04]
Monday, March 23, 10:50 AM – 11:40 AM PDT | Moscone West 3011
AI vulnerability discovery is no longer speculative. AI ranks #1 on HackerOne’s leaderboard. DARPA’s AIxCC uncovered 54 vulnerabilities in hours. APT28 reportedly folds LLMs into malware, closing the exploitation gap. This session will examine evidence of this shift and provide concrete strategies to prepare for the coming flood of vulnerabilities.
Heather Adkins, VP, Security Engineering, Google, and RTF Steering Committee member
HD Moore, Founder, runZero
Gadi Evron, Founder Knostic
Belonging in Cyber: Building a Trusted Community – [CXN-M06]
Monday, March 23, 1:10 PM – 2:00 PM PDT | Moscone West 2016
This session will bring together different affinity groups in cybersecurity to help attendees build trusted networks. Come meet industry influences who have successfully built thriving networks and learn how to build a supportive community.
Lynn Dohm, Executive Director, Women in Cybersecurity
Megan Jacquot, Cybersecurity Engineer, Diana Initiative
Lauren Zabierek, Senior Adjunct Advisor, Institute for Security and Technology
Larci Robertson, President, Women in Security
Rebekah Skeete, COO, BlackGirlsHack
Rolanda Small, Executive Director, Cyversity
AI Use Cases for Offense/Risk Assessment – [CXN-M07]
Monday, March 23, 2:20 PM – 3:10 PM PDT | Moscone West 2016
This interactive session on offensive security and risk assessment will explore how LLMs and automated agents are transforming threat modeling and rapid discovery. Participants will exchange insights on specific tooling and real-world use cases for identifying vulnerabilities at scale.
Bryson Bort, Founder, SCYTHE, and Adjunct Senior Technical Advisor, Institute for Security and Technology
Jake Williams, VP, R&D, Hunter Strategy
Tuesday

We Think It Was Them: The Perils of Attribution in Public Statements – [LAW-T01]
Tuesday, March 24, 8:30 AM – 9:20 AM PDT | Moscone West 2001
Attribution in cyberattacks is rarely clear, yet organizations face pressure to name suspects. This panel will examine legal, diplomatic, and reputational risks, strategies for careful communication, and how to respond when others attribute on someone’s behalf. The panel will discuss how to protect credibility while aligning with broader public interest goals.
Megan Stifel, Chief Strategy Officer, Institute for Security and Technology
Brett Callow, Managing Director, FTI Consulting
Sam Sabin, Cybersecurity Reporter, Axios
Mike Egan, Partner, Cooley LLP
Activate Industry!: Moving Beyond Defense to Disruption and Active Defense – [KEY-T04W]
Tuesday, March 24, 10:50 AM – 11:10 AM PDT | Moscone West Street Level
Adversaries are evolving their tactics and developing dangerous AI attacks at scale. The current plan—to hope things improve—is not working. Companies must move beyond mere information sharing and embrace a mandate to proactively disrupt threat actors and impose real costs on their operations. Come learn how Google is disrupting threat actors through active defense.
Sanda Joyce, VP, Google Threat Intelligence, Google Cloud, and RTF Steering Committee member
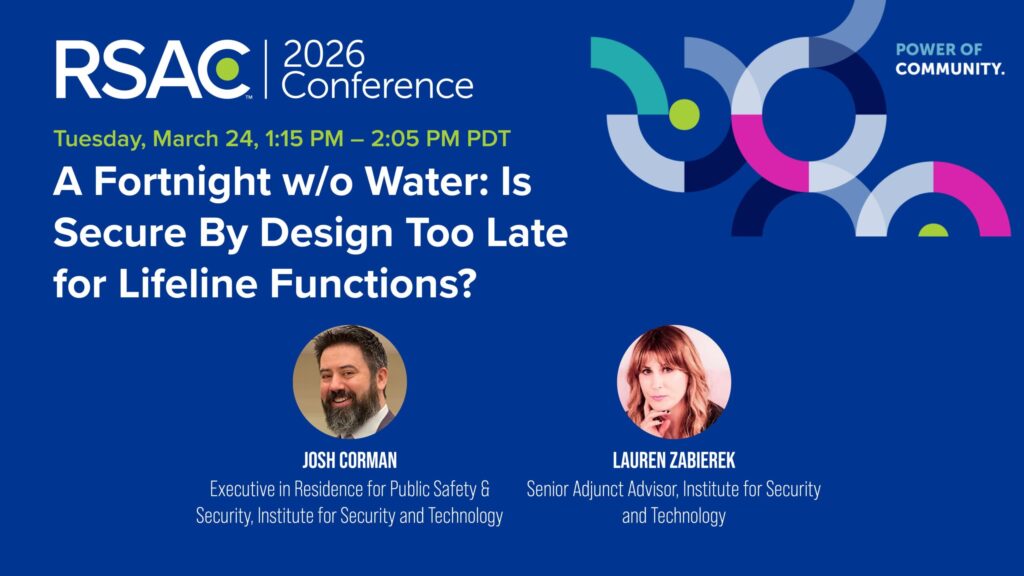
A Fortnight w/o Water: Is Secure By Design Too Late for Lifeline Functions? – [CIT-T09]
Tuesday, March 24, 1:15 PM – 2:05 PM PDT | Moscone West 2006
The clock is ticking toward 2027—a looming flashpoint in US-China tensions over Taiwan with state-backed actors already prepositioned in US critical infrastructure. This debate will start with an uncomfortable truth: It may already be too late to secure the devices that run lifeline functions. It doesn’t mean there are no options. The session will conclude with what can be done, for whom, by when.
Josh Corman, Executive in Residence for Public Safety & Security, Institute for Security and Technology
Lauren Zabierek, Senior Adjunct Advisor, Institute for Security and Technology

The Cyber House Rules: Perspectives on the 2026 Congressional Agenda – [PNG-T10]
Tuesday, March 24, 2:25 PM – 3:15 PM PDT | Moscone West 2007
Step into the shoes of Congressional staff charged with overseeing the US government’s enterprise systems and setting the agenda for CISA, ONCD, and other key agencies. This panel discussion features leaders from two of the principal cyber committees in the House and will cover legislative developments on information sharing, regulatory harmonization, the CVE program and more.
Nicholas Leiserson, Senior Vice President for Policy, Institute for Security and Technology
Moira Bergin, Staff Director (Minority), Subcommittee, Cybersecurity & Infrastructure Protection, Committee on Homeland Security
Graham Harwood, Professional Staff Member, US House of Representatives
Roland Hernandez, Staff Director, Subcommittee on Cybersecurity, US House of Representatives
How Agentic AI Broke Threat Intelligence and How to Fix It – [PART2-T10]
Tuesday, March 24, 2:25 PM – 3:15 PM PDT | Moscone South Esplanade 154
Advanced adversaries now use agentic AI to execute attacks at machine speed, often exploiting LLM weaknesses for mass disruption. Traditional TI, reliant on human analysis of massive datasets and static IOCs, can’t keep pace. This talk will show how recent AI attacks expose TI’s failures and detail the blueprint to evolve TI into an adaptive intelligence layer that empowers analysts to stay ahead.
Michael Daniel, President and CEO, Cyber Threat Alliance, and RTF Co-chair
Raja Mukerji, Co-founder and Chief Scientist, ExtraHop Networks
Wednesday

How 3rd Party Risk & a Teen Hacker Got K-12 Cyber into the Situation Room – [CIT-W01]
Wednesday, March 25, 8:30 AM – 9:20 AM PDT | Moscone West 2006
Five cyber incidents impact K-12 schools each week, with ransomware disrupting learning nationwide. Yet the real risk comes from a few 3rd-party vendors that districts rely on for critical operations—a risk made clear by the 2024 PowerSchool data extortion. This session will unpack how federal, state, and local leaders mobilized during the crisis and share steps to protect students and teachers.
Michael Klein, Senior Director for Preparedness and Response, Institute for Security and Technology
Rich Mogull, Chief Analyst, Cloud Security Alliance
Wednesday, March 25, 9:40 AM – 10:30 AM PDT | Moscone West 2007
Andrew Boyd, CEO, REDLattice and Member, IST Board of Directors
Rob Joyce, Venture Partner, DataTribe
Katie Gray, Senior Partner, In-Q-Tel
John Carlin, Partner, Paul Weiss
Will Pearce, CEO & Co-Founder, Dreadnode
Thursday
Why Is It Running Window XP? – [VLG-R03]
Thursday, March 26, 10:50 AM – 11:40 AM PDT | Moscone South 204 Briefing Center
OT networks power critical infrastructure, yet many facilities still depend on Windows XP, Windows 7, unpatched PLCs, and aging HMIs running essential processes. This talk will explore why these legacy systems remain, the operational and cybersecurity risks they create, and realistic strategies to secure and modernize environments without disrupting production.
Bryson Bort, Founder, SCYTHE, and Adjunct Senior Technical Advisor, Institute for Security and Technology
Thomas VanNorman, Co-Founder, ICS Village



