Dear Fellow Protectors,
Is it too late for secure-by-design? That provocative question was at the heart of Josh’s presentation at the RSAC Conference this year. In a mock debate with Lauren Zabierek, one of the former leads for the Secure-by-Design program at CISA, Josh took the position that projects like U27 and its embrace of INL’s Cyber-Informed Engineering approach may be the only realistic ways to shore up lifeline sectors in the immediate future—especially for the majority Have Nots.
At U27, we believe that society is too dependent on undependable technology. One way to address this challenge is to make technology more dependable. That’s a key goal of the Secure-by-Design movement, which aims to ensure security considerations are baked into products, not bolted on after the fact.
However, there are two core problems with Secure-by-Design in the lifeline sector context. The first is capacity. When you’re what Josh calls “Target Rich, but Cyber Poor” and you are operating at or below the “Security Poverty Line,” as our friend Wendy Nather says, rolling out the safest available technology and fixes may be out of reach. Not only are the changes often more than owners and operators can shoulder, the service providers they depend upon may not be willing or able to assist without changes to existing contracts.
The other challenge is “legacy” and technical debt. It would be one thing if a one-time infusion of resources could help migrate utilities or hospitals from their current systems to more secure-by-design ones. But, in most cases, the systems today aren’t current. When it comes to operational technology, they may be decades old—and replacement is much more complicated than just buying a new software license.
Where we are out of time for more dependable technologies, our approach starts with adding in resilience first, relying more heavily on consequence reduction and on off-network engineering solutions, reducing elective connectivity, and practicing manual operations in the event of unexpected downtime. Where such solutions can be applied, like pressure sensor arrestors for a water system, they’re almost always quicker and cheaper than a complete tech stack refresh. As conflicts continue to rage around the world, one thing we don’t have is the luxury of time. U27 is ready to meet the moment today.
Of course, the twist in Josh’s presentation was that you really need both. Maybe the best time to have done secure-by-design was 16 years ago, when Josh published the Rugged Software Manifesto (or even 40+ years ago during the Therac-25 losses of life). The next-best time for Secure-by-Demand… is today.
Thank you to those of you who joined us at RSAC for the first version of this debate and the framework! To continue the conversation, we’ve invited Lauren & CISA to build upon it this June in DC! Thought-provoking conversations are our stock-in-trade at the Critical Effect conference, which is just eight weeks away! Register now to join us in Washington, DC, June 17-18 and hear from protectors and policymakers about how to supercharge our efforts to keep our communities safe. And, as ever, join us on the U27 Slack channel or nominate a community to join the pilot!
Joshua Corman
Executive in Residence for Public Safety & Resilience
Stephanie Ross
Managing Program Director for Public Safety & Resilience
Nicholas Leiserson
Senior Vice President for Policy
Critical Effect DC Conference
Join Us: June 17-18
Registration is now live! With 2027 getting closer, we will hear from speakers that are prioritizing real, actionable impact.
Critical Effect DC provides a unique platform for leading voices in ICS and cybersecurity to engage with policymakers, think tanks, and the media, while facilitating hands-on experiences and encouraging informed, actionable discussions. Unlike most cyber-related events, our center of gravity is zeroed in on National Security & Public Safety / Human Life. Presented by ICS Village, in partnership with the Institute for Security and Technology’s UnDisruptable27 project and Akin.
When: Wednesday, June 17 – Thursday, June 18, 2026
Where: Akin, 2001 K Street NW, Washington DC 20006
How to join: Register on Eventbrite
Where We'll Be
May 28 – West Region Cyber Civil Defense Summit, hosted by UC Berkeley, in Scottsdale, AZ
May 31 – June 2 – Josh will be co-presenting with Casey John Ellis at NaClCON: The History of Hacking/Cybersecurity Conference
June 17-18 – Critical Effect in Washington, DC
June 21-24 – AWWA Annual Conference & Expo (ACE26), Washington, DC
August 3-5 – BSides Las Vegas, I Am The Cavalry Track, Las Vegas, NV
September 16 – 1 Day Tech Innovator’s Critical Effect in Sacramento, CA
Where We've Been
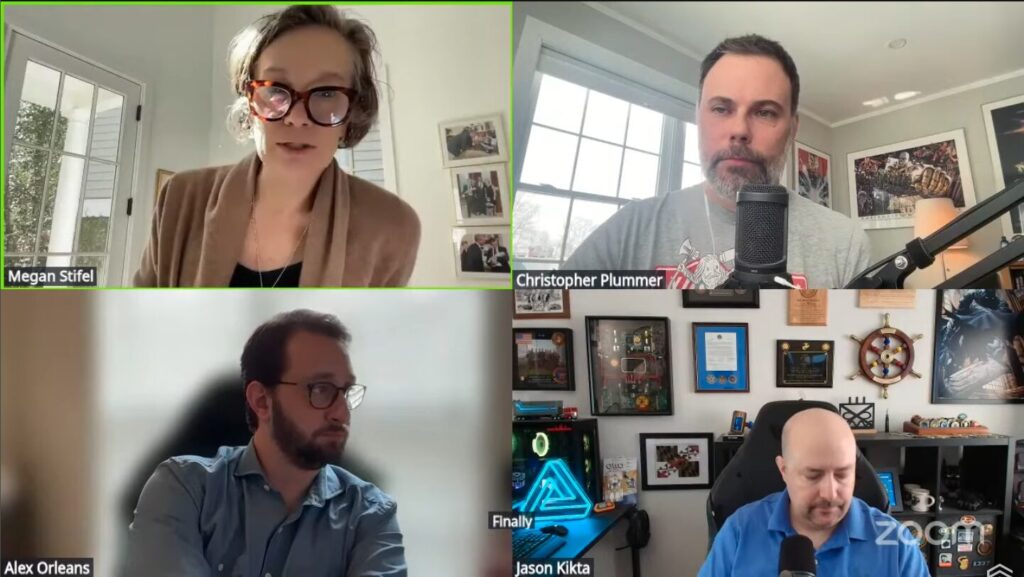
On March 13, IST’s Megan Stifel, UnDisruptable27 volunteer Chris Plummer, and 2 other experts hosted a live webinar attempting sense-making of the Iranian-affiliated hacking of Stryker.
On March 17, Josh joined Dr. Kevin Fu’s graduate course at Northeastern University to give a guest lecture on life-safety, cyber-physical threats to healthcare.
On March 19, Josh hosted an UnDisruptable27 special edition of the Boston Security Meetup at the NERD Center in Cambridge, MA, with personal calls to action in the home of the Minute Men.
On March 24, Josh co-delivered a “debate” (packed w/ Taylor Swift lyrics) at RSAC on the most realistic & effective strategies for most life-line critical infrastructure operators against the coming storms of Volt Typhoon: “Critical Infrastructure: A Fortnight w/o Water: Is Secure by Design Too Late for Lifeline Functions?”
On April 16, Josh addressed the Irregular Warfare Center’s Military Medicine Summit at the Mayo Clinic in Minnesota, exploring the impacts of hybrid conflict on homeland healthcare capacity (a much heavier subject devoid of Taylor Swift lyrics).
Our Media Diet
Fighting the Water Hackers, Episode #193 – Josh joined the Reimagining Cyber podcast to provide real world perspectives on cybersecurity and bring some heavy candor on growing concerns from the Typhoons and now Iran.
The Fight Comes to Our Shores – Review of the Iranian-affiliated hacking of Stryker in a live webinar by IST’s Megan Stifel, UnDisruptable27 volunteer Chris Plummer and 2 other experts.
Cyber Informed Engineering: Moving Beyond the Firewall – On this last episode of Hack the Plant’s season 5, Bryson Bort sits down with Andrew Ohrt, Resilience Director at West Yost Associates and U27 volunteer, to walk through the invisible nature of water systems, the impact of data centers on utility resilience and how Cyber-Informed Engineering protects our most essential resource.
CISA Alert: Iranian-Affiliated Cyber Actors Exploit Programmable Logic Controllers Across US Critical Infrastructure – U.S. organizations should urgently review the tactics, techniques, and procedures (TTPs) and indicators of compromise (IOCs) in the April 7 CISA alert, and apply the recommendations, to reduce their risk of compromise.
Rural Water’s Ripple Effect: National Security, Cyber Threats, and the Future of Water – NRWA & Cyber Civil Defense expert Nicole Tisdale published a policy paper analyzing how the Water Sector workforce is a critical component of national security.
HBO’s ‘The Pitt’ nails how hospital cyberattacks create chaos, endanger patients and disrupt critical care – In The Conversation, Jeffrey Tully and Christian Dameff reflect on The Pitt’s realistic depiction of the effect of a cyber attack on a hospital emergency room. Although policy and legal efforts aim to stop these malicious security breaches, they are growing more common as hospitals adopt remote health care delivery and hackers adopt artificial intelligence.
Anthropic’s Mythos preview and Project Glasswing have kicked up quite the stir, with implications on life-line critical infrastructure disruptions which could both be as serious as Volt Typhoon and come sooner. A group of IT Security Experts have also offered their suggested adaptations. UnDisruptable27 has remaining “as-of-yet unaddressed concerns” – and will soon discuss them more openly.
Iran is trying to turn off America’s water – An op-ed by fellow Cyber Civil Defense grantee Jake Braun of DEF CON Franklin reflects on the threat faced by our nation’s water utilities [subscription required]
Gus Serino on the Efforts of a Massachusetts Water Cybersecurity Collaborative – On the Nexus Podcast, Gus Serino, President of I&C Secure, Inc., explains how he organized a collaborative of water and wastewater utilities to share resources and cybersecurity information to help reduce risk.
Previous editions

#4: This is why UnDisruptable27 exists
In the aftermath of last week's attack on a U.S. medical device manufacturer by a pro-Iran regime hacktivist group, UnDisruptable27's newsletter reflects on its very reason for existence: "to ensure that our communities can take the punch that's coming, even if it's from our most capable foes."

#3: Innovate narrowly, scale widely
From working with small and local communities to connecting with policymakers, UnDisruptable27’s mantra is to innovate narrowly and scale widely. As the team continues working to identify potential communities for piloting our cyber-informed, engineering first approach, we’re turning our attention to the policy sphere.

#2: Save the Date for Critical Effect 2026
In the second issue of our newsletter, save the date for Critical Effect 2026, listen to the latest episode of Hack the Plan[e]t and other featured podcasts, and find out where to see us .

#1: Happy Holidays from U27
In the inaugural edition of the UnDisruptable27 newsletter, learn how to participate in FrostyVolt’25, where to find us, and what we’ve been reading.