Late 2016 and early 2017 were an interesting time on Capitol Hill. As a staffer for one of the visionary cybersecurity leaders in Congress, I heard regularly from constituents and industry about a range of technology topics. Unsurprisingly, what I heard normally focused on Congressional bills, the latest changes at various federal agencies, or even state-level legislation. However, as the 115th Congress convened, something strange happened. Nearly every tech-related meeting I had brought up a policy that had no room for input from U.S. policymakers or citizens: the EU’s General Data Protection Regulation, or GDPR. What, these petitioners asked me, was the Congress going to do about it?
The answer, of course, was nothing. What could we do? The policy had been developed in Europe with input from European elected leaders. Despite years of effort, the United States still lacked any comparable national privacy regulation that we could point to as an example of how to better address the issue comprehensively. The constituents coming through our office were right to be concerned that Europe would set the bar for privacy going forward. And they were right to think that the defaults, scope, and values embodied in the GDPR would not necessarily reflect their views.
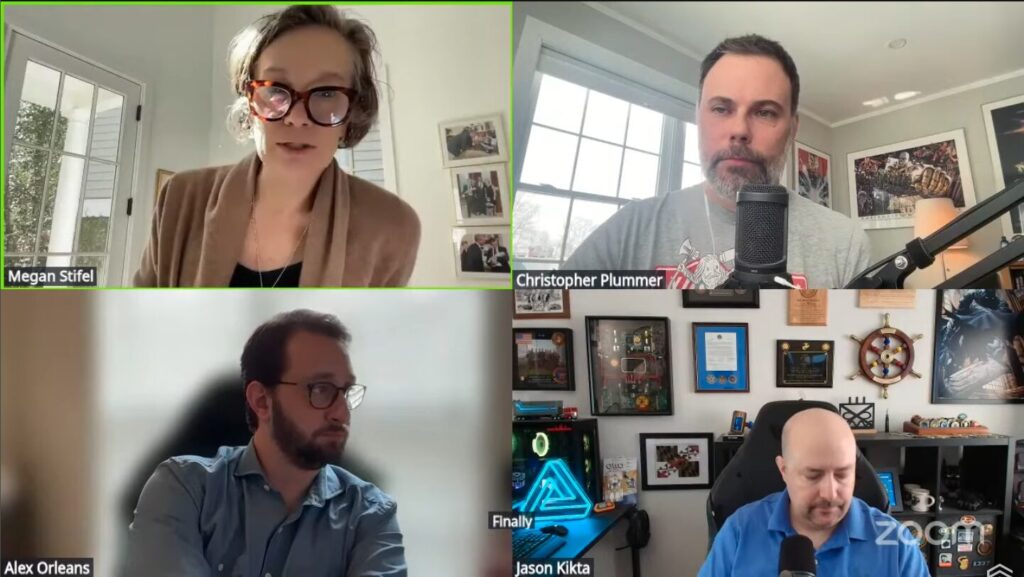
My time in Congress answering constituent questions about the GDPR immediately came to mind as I reviewed Taylor Roberts’s new analysis for IST, “Comparative Analysis of National and Regional Product Cybersecurity Frameworks.” Though the world currently has few active comprehensive product cybersecurity regimes, Roberts paints a picture of the numerous jurisdictions currently looking to develop their own, each with different scopes, vulnerability and incident disclosure obligations, product lifecycle requirements, and types of enforcement. The product cybersecurity regulatory landscape in 2028 will look far different to a manufacturer or developer of software—but it’s not clear how much U.S. industry or policymakers have woken up to that fact.
While Europe was busy instituting the GDPR in 2018 and passing the Cyber Resilience Act in 2024–the most comprehensive product cybersecurity legislation to date–U.S. policymakers are failing to keep up. Now, in addition to Europe, we see schemes in theUnited Kingdom, Singapore, Australia, Korea, and Japan. In contrast, there are four separate U.S. proposals Roberts highlights in his overview table; none have advanced past the draft phase (I have thoughts on the lethargy of the FAR Council). Cybersecurity is too important to our national and economic security—and the U.S. too vital a hotbed for innovation—for us to cede leadership on ensuring software can withstand the threats against it. This imperative only grows as AI stands to dramatically expand the prevalence of software in all aspects of our life, and as malicious actors increasingly exploit software vulnerabilities.
Thankfully, it is not too late for policymakers to act. While the United States has fallen behind in developing its own product cybersecurity requirements, American officials can still demonstrate leadership by pushing for regulatory alignment on this topic. As I have testified, reducing compliance burden without lowering the bar for security and safety is the rare win-win in policymaking: it reduces costs and improves cybersecurity outcomes. As the world’s governments near the finalization stages of their product cybersecurity regimes, we are in a critical period at an inflection point. Now is the time to ensure alignment and to push for mutual recognition, broadly-recognized certification, or other means to reduce duplicative compliance activities.
As the administration considers how to implement the “Promote Common Sense Cyber Regulation” pillar of the 2026 National Cyber Strategy, Roberts’s new paper has given us an invaluable tool for advancing international dialogue on regulatory alignment. By decomposing the various regulatory frameworks into their constituent parts, he shows that, in most cases, there is convergence on the types of controls included in product cybersecurity regimes. While many of the specifics differ, the broad goals do not. There is hope.
But hope, as they say, is not a plan. We are nearing the event horizon, the point of no return, where bureaucratic inertia will calcify these dueling and duplicative product cybersecurity approaches. Roberts’ paper is fuel to escape this fragmented future; however, it is not sufficient. Leadership is needed to alter course. It’s time for U.S. policymakers to link arms with their UK colleagues and chart a new path for regulatory harmonization.