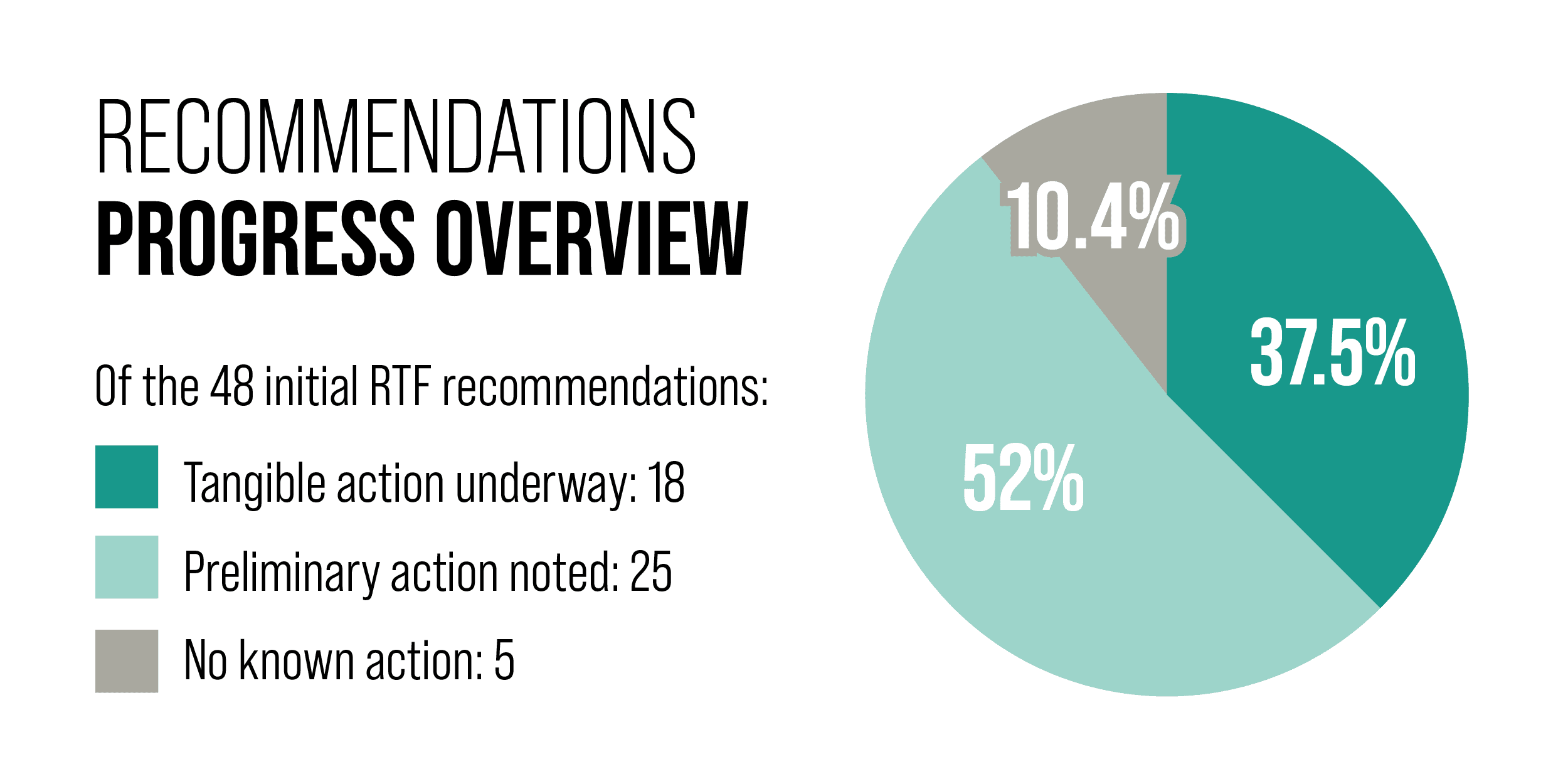
In the 6 months since the publication of the Ransomware Task Force (RTF) Progress Report this May, we have seen a great deal of action to combat ransomware, but we have also seen the scale of the threat continue to grow, even as stakeholders continue to focus on it.
Experts continue to sound the alarm about the scale and scope of the ransomware threat. In a June speech, the head of the UK’s National Cyber Security Centre (NCSC), Lindy Cameron, said, “even with a war raging in Ukraine – the biggest global cyber threat we still face is ransomware.” A report by researchers at Barracuda Networks corroborates this claim, noting that the volume of ransomware attacks spiked to 1.2 million per month in 2022.
Despite the looming threat of ransomware, there has been significant progress in the fight against the ransomware threat. The June joint European Union and United States ransomware workshop at the Hague, and October 31-November 1 International Counter Ransomware Initiative Summit indicated strong international commitment to counter ransomware. Meanwhile, law enforcement continues to seize ransom payments. In this December 2022 progress update, we will outline major progress seen across the ransomware ecosystem and identify key areas to focus our efforts moving forward.
Deter
Governments and industry continue to develop authorities, programs, and capabilities that work to secure critical sectors and build relationships domestically and abroad to facilitate enhanced communication and coordination in addressing cybersecurity and ransomware-related risks.
Meaningful progress has been made in the last six months, including:
- Action 1.2.3, Conduct a sustained, aggressive, public-private collaborative anti-ransomware campaign.
- In August 2022, the Department of Homeland Security (DHS) announced funding allocations for FY2022 preparedness grants. These will prioritize six critical areas, including cybersecurity. The grant programs provide funding to state, local, tribal and territorial (SLTT) governments, nonprofit agencies, and the private sector to build and sustain capabilities to strengthen cybersecurity.
- Actions 1.1.1, Issue declarative policy through coordinated international diplomatic statements that ransomware is an enforcement priority, 1.1.2, Establish an international coalition to combat ransomware criminals, and 1.1.4, Convey the international priority of collective action on ransomware via sustained communications by national leaders.
- The second Counter Ransomware Initiative Summit, held October 31 and November 1, 2022, represents an important step toward signaling internationally that ransomware remains a top enforcement priority. Additionally, multiple high level government statements, such as the September Quad Foreign Ministers Statement on Ransomware, continue to underscore that senior leaders see tackling ransomware as a high priority.
The RTF lauds this progress and welcomes declaratory statements such as the International Counter Ransomware Initiative joint statement.
Disrupt
The majority of ransomware payments involve cryptocurrencies and a subsequent network of exchanges, mixers, tumblers, and other entities. The obscure nature of these payments, together with low incident reporting rates, makes payment attribution and subsequent disruption difficult. Governments are working to address this issue in a number of ways, including by identifying ways to apply existing regulatory frameworks to the cryptocurrency ecosystem or applying sanctions to specific exchanges.
Despite the challenges posed by the cryptocurrency ecosystem, significant progress has been made in the last six months:
- Action 2.1.1, Develop new levers for voluntary sharing of cryptocurrency payment indicators.
- In November, IST and the Cyber Threat Alliance (CTA) released a proposed Cyber Incident Reporting Framework, which identifies critical opportunities to share information about cryptocurrency payments.
- Action 2.1.3, Incentivize voluntary information sharing between cryptocurrency entities and law enforcement.
- A first step in achieving this goal is to develop a clear understanding of the ransomware payment ecosystem. In November, IST released “Mapping the Ransomware Payment Ecosystem: A Comprehensive Visualization of the Process and Participants,” a complex visualization of the information, actors, and entities involved in the ransom payment process, which addresses this gap, and advocates for information sharing between cryptocurrency businesses and law enforcement.
- Actions 2.1.3, Incentivize voluntary information sharing between cryptocurrency entities and law enforcement and 2.1.4, Centralize expertise in cryptocurrency seizure, and scale criminal seizure processes.
- In September, the Department of Justice released a report outlining the role of law enforcement in “Detecting, Investigating, And Prosecuting Criminal Activity Related To Digital Assets.” This report came on the heels of several cryptocurrency seizures, including the July seizure of approximately 500,000 in ransom payments demanded by North Korean state-sponsored ransomware attackers. Further, the aforementioned “Mapping the Ransomware Payment Ecosystem: A Comprehensive Visualization of the Process and Participants” sheds light on the role of cryptocurrency in illicit ransomware-related payments, and may be used to help identify future opportunities for disruptive collaboration.
Prepare
Governments, critical infrastructure providers, and small and medium-sized entities (SMEs) continue to aim to drive greater adoption of preparedness best practices at scale. Part of the challenge is providing actionable guidance tailored to organizations’ needs and contexts without adding additional complexity that they may not have the bandwidth to interpret and implement. Yet resource constraints and limited technical maturity hinder organizational progress towards preparing for ransomware attacks.
Nevertheless, governments in particular are making headway:
- Actions 3.1.2, Develop complementary materials to support widespread adoption of the Ransomware Framework, and 3.2.1 Develop business-level materials oriented toward organizational leaders.
- In July, IST’s RTF released the Blueprint for Ransomware Defense, a curated subset of essential cyber hygiene Safeguards that draw from the Center for Internet Security Critical Security Controls® (CIS Controls®) v8. This fall, IST hosted a 5-part webinar series to provide additional guidance and insight on implementing the Blueprint for SMEs.
- Action 3.3.1, Update cyber-hygiene regulations and standards.
- CISA included the RTF’s Blueprint for Ransomware Defense on stopransomware.gov, a “one-stop location” for resources to support regulatory compliance and best practice adoption.
- Action 3.3.3, Require managed service providers (MSPs) to adopt and provide baseline security measures.
- In May, CISA, together with cybersecurity authorities of the United Kingdom (NCSC-UK), Australia (ACSC), Canada (CCCS), New Zealand (NCSC-NZ), released a joint cyber advisory which urges MSPs and their customers to implement baseline security measures and operational controls.
- Actions 3.4.1, Highlight ransomware as a priority in existing funding provisions, 3.4.2, Expand Homeland Security Preparedness Grants to encompass cybersecurity threats, and 3.4.3, Offer local government, SLTTs, and critical NGOs conditional access to grant funding for compliance with the Ransomware Framework.
- As noted above, in August, DHS allocated funding for preparedness grants for FY2022.
- The RTF applauds this progress and encourages the United States and other countries to continue to invest in improving cybersecurity, to align policy and operational efforts across sectors and countries, and to maintain pressure on ransomware actors to deter them from employing ransomware attacks.
Respond
No matter how effective deterrence, disruption, and prevention efforts become, some percentage of attacks will inevitably succeed. To prepare for attacks when they occur, the RTF called for improving the ability of individuals, organizations, and society to respond to successful ransomware attacks.
The United States has made some progress in the last six months, including:
- Action 4.1.3, Increase government resources available to help the private sector respond to ransomware attacks.
- CISA added IST’s RTF Blueprint for Ransomware Defense to its website. The Blueprint encourages SMEs to establish and maintain an enterprise process for reporting incidents, and designate personnel to manage incident handling, among other measures.
- Action 4.1.4, Clarify United States Treasury guidance regarding ransomware payments.
- In August, for the first time, the Office of Foreign Assets Control (OFAC) sanctioned virtual currency mixer, Tornado Cash, and in September sanctioned ten individuals and two entities for their roles in malicious cyber activity, including ransomware attacks. These moves signal a crackdown on ransomware actors, non-compliant cryptocurrency mixers, and other entities in the ecosystem, thereby restricting the available options for ransom payments and their subsequent laundering.
- Action 4.2.2, Create a standard format for ransomware incident reporting.
- As noted above, IST and the Cyber Threat Alliance published a Cyber Incident Reporting Framework, which was submitted to inform CISA’s Request for Information (RFI). While this structure has yet to be adopted, the CISA rulemaking process is a critical first step in developing a standardized reporting process.
- Action 4.2.3, Encourage organizations to report ransomware incidents.
- IST and CTA’s Cyber Incident Reporting Framework, submitted to inform CISA’s RFI, advocates for shifting the reporting culture to encourage reporting. The form is designed to be easy to understand and iterative to encourage voluntary incident reporting and information sharing.
We applaud the progress made by the U.S. and other governments, industry, and civil society in the fight against the ransomware threat. However, as the scale of these incidents continues to grow, there is more to be done.
Next Steps
It is critical that we continue to improve information sharing, through public/private collaboration, and by streamlining, harmonizing, and simplifying cyber incident reporting. The Cyber Incident Reporting Framework–described above–acts as a roadmap to establishing a more effective reporting system.
Further, efforts to disrupt ransomware would not be complete without a focus on the underlying incentive structure. Disrupting the ransomware business model by adding friction to the ransomware payment process is a critical net step to achieving this aim. The recently released “Mapping the Ransomware Payment Ecosystem: A Comprehensive Visualization of the Process and Participants” enables that work by depicting the process itself and the entities and information involved.
Finally, continuing international engagement and harmonizing efforts across borders is critical to mitigating the ransomware threat. Many of the underlying tools and technologies that enable ransomware, like cryptocurrency, are distinctly international. Without an equally international mitigation strategy, we cannot successfully deter, disrupt, prepare, or respond to the threat of ransomware. Such a strategy should focus on implementing AML/CFT regulations on cryptocurrency entities and enable information sharing between national governments to support operational collaboration.
The IST staff, along with experts from government, civil society, and the private sector, continue to implement the Ransomware Task Force’s recommendations. In 2023, IST’s RTF will build out the Ransomware Payment Ecosystem Map, using the insights it provides to identify opportunities for stakeholders to share information and interrupt the ransomware payment cycle. We also plan to explore ways to strengthen cybersecurity more generally, including via open source software security and by bolstering the business case for investing in resilient systems. We are looking forward to tackling this agenda and more in 2023.