On Wednesday, March 11, a pro-Iran regime hacking group claimed to have wiped 200,000 devices of a major U.S. medical device manufacturer. Early press reports indicated that operations at the manufacturer, Stryker, had been affected. While pro-Iran cyber operations have been ongoing in the Middle East since the onset of the war in Iran, last week’s attack marked the first significant incident on United States soil.
Many unknowns remain, but one thing is certain: in bringing the fight to the homeland, cyber is the weapon of choice.
The Institute for Security and Technology’s UnDisruptable27 Initiative has been preparing for this kind of attack on domestic infrastructure for the last two years, working to equip communities who might become targets with the information, tools, and support they need to defend themselves. Now in its second phase, UnDisruptable27 is connecting with the owners and operators of small and rural water utilities to ensure their systems are resilient to cyber attacks of all kinds.
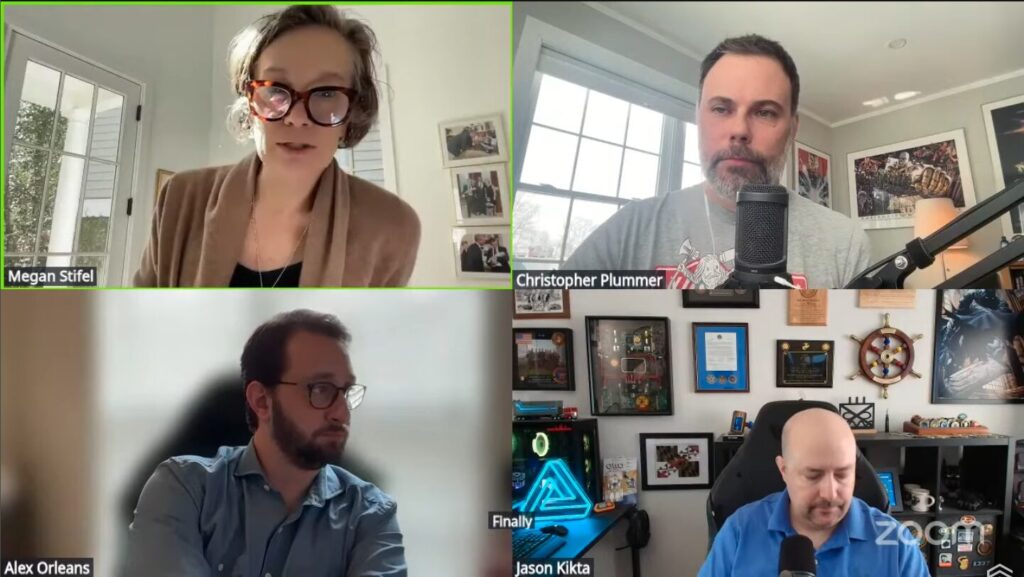
On Friday, IST convened a pop-up webinar with friends and adjuncts to break down the attack, consider its implications, and answer pressing questions from the community.
We came to the webinar looking to answer some key questions about the incident: What do we know about what happened, and who carried out this destructive attack? What are the potential motivations behind the targeting? How does it compare to past cyber operations? And how should policymakers and critical infrastructure operators respond?
IST Chief Strategy Officer Megan Stifel moderated the discussion with panelists Jason Kikta, Chief Technology Officer at Automox and Adjunct Senior Technical Advisor at IST; Alex Orleans, Head of Threat Intelligence at Sublime; and Christopher Plummer, Senior Cybersecurity Architect at Dartmouth Health.
Drawing on his background in threat intelligence, Alex framed the context behind the Stryker attack, explaining that pro-Iran hackers often select targets like medical technology suppliers because they know it will incite fear.
“As is tradition among Iranian actors, they’re trying to inflict psychological effects wherever they can,” he said.
While the attack did result in disruptions to Stryker’s internal systems nationwide, there are no reports of effects to the company’s connected digital technologies.
In fact, Christopher shared, many healthcare cyber experts first learned of the attack online before reaching out to Stryker for official confirmation. The company’s products range from hospital beds to a surgical robot popular in the orthopedic industry, and Stryker is only one of dozens of third parties who might supply a single hospital. It wasn’t as easy as simply finding the Stryker logo in their environments, he explained.
“It is a diverse spectrum of impact, and so we’ve forced ourselves to itemize all of these impacts.” Chris said. “We have two charges: patient safety and continuity of operations as a hospital. Those are the two most important things in our world. They drive everything. If either of those are in doubt, we have to make just very, very frustrating and challenging choices about lines of care.”
Speaking to the actors’ motivations, Jason noted that the attack is consistent with pro-Iran groups’ histories of selecting highly public but non-government targets, like Sands Casino in February 2014.
“Because they believe the regime is going to survive, they’re going to focus on things where they can develop access quickly through phishing or hitting something that’s publicly exposed and vulnerable,” Jason said. “If they were focused on regime survival, they would [target defense contractors]…They’re going to go after what they perceive, probably correctly, is our soft underbelly.”
Discussing whether Stryker’s data might be commoditized, selectively leaked, or used for access development, the panelists disagreed. Jason said he expected to see the data on the black market, while Alex noted that pro-Iran actors have not sold extorted data before.
“I think access development is the most likely thing they’ll do,” he said.
Finally, what can at-risk service providers do to prepare themselves against similar attacks? Christopher emphasized attack service management.
“This is a time to, again, revisit assumptions about the way you do business with other entities, and afford them remote access, and provide access to remote workers, all manners of ways into your environment,” he said.
Alex concurred, adding: map your networks.
“The one thing that attackers always have a better version of than you do, it’s your network map. If you have a meaningful network map, you’re going to surface the parts of your attack surface that you didn’t know existed,” he said.