Last week’s attack on a U.S. medical device manufacturer demonstrates precisely why UnDisruptable27 exists
Dear Fellow Protectors,
In January, we shared some thoughts about the rapidly evolving geopolitical landscape. Over the last month, it’s evolved even more, and in ways that continue to showcase the destructive intent of malign actors… and our over-reliance on undependable technology.
On Wednesday, pro-Iran hackers hit a U.S. company with a wiper attack. A hacktivist group—one that is publicly aligned to the Iranian regime and may even be directly linked to the Iran Ministry of Intelligence and Security— has claimed credit for the attack, framing it as retaliation for the U.S. and Israeli bombing campaign.
We don’t know why the company, a major medical device and supply manufacturer, was targeted. We don’t know what the malicious actors aimed to get out of the operation, which reportedly affected 200,000 devices. What we do know is that, in a time of war, cyber effects were the tool of choice for bringing the fight to the U.S. homeland.
This is dangerous. It is not surprising. Our work at U27 is predicated on the fact that, whether for psychological impact or operational disruption, our adversaries will turn to cyber means to hit us at home. We exist to ensure that our communities can take the punch that’s coming, even if it’s from our most capable foes.
On Friday, IST friends and adjuncts, including one of our UnDisruptable27 allies, Dartmouth Health senior cybersecurity architect Christopher Plummer, participated in a webinar breaking down some of the initial implications, and what organizations should be doing about it.
We don’t yet know the fallout from this latest attack. Above all, we do know that it continues to showcase our vulnerability. And we know that others are watching to see how we respond.
So, now is the time to do your part to protect your family and neighbors. Nominate your community to be part of our cohort. Volunteer your time to help co-create concrete engineering solutions to hard problems. Submit a talk for Critical Effect. And then come join us on June 17-18 in Washington, DC.
Joshua Corman
Executive in Residence for Public Safety & Resilience
Stephanie Ross
Managing Program Director for Public Safety & Resilience
Nicholas Leiserson
Senior Vice President for Policy
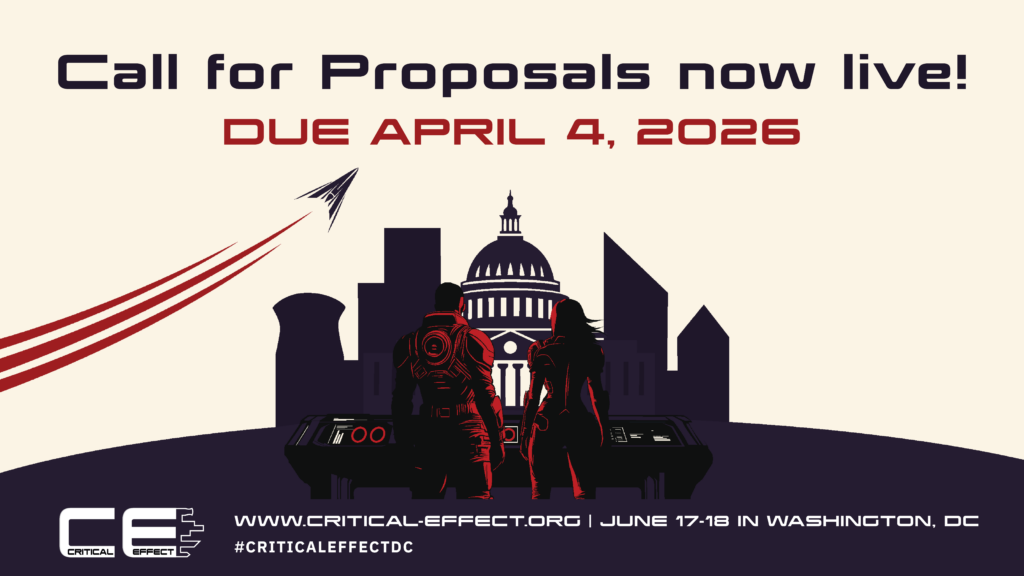
Critical Effect DC Conference
*NEW* Save the Date: June 17-18
Mark your calendars! Our two-day Critical Effect Conference is coming back to Washington, DC. With 2027 getting closer, we are prioritizing ideas that lead to real, actionable impact.
Critical Effect DC provides a unique platform for leading voices in ICS and cybersecurity to engage with policymakers, think tanks, and the media, while facilitating hands-on experiences and encouraging informed, actionable discussions. Unlike most cyber-related events, our center of gravity is zeroed in on National Security & Public Safety / Human Life. Presented by ICS Village, in partnership with the Institute for Security and Technology’s UnDisruptable27 project and Akin.
When: Wednesday, June 17 – Thursday, June 18, 2026
Where: Akin, 2001 K Street NW, Washington DC 20006
How to join: Submit a proposal by April 4, 2026. Stay tuned for registration details!
Where We'll Be
- March 19 – Josh is hosting a special edition of the Boston Security Meetup at the NERD Center in Cambridge, MA from 6-9pm
- March 24 – Josh co-speaking on Volt Typhoon at RSA Conference in San Francisco: “Critical Infrastructure: A Fortnight w/o Water: Is Secure by Design Too Late for Lifeline Functions?
- June 17-18 – Save the Date for the Critical Effect Conference in Washington, DC
- June 21-24 – AWWA Annual Conference & Expo (ACE26), Washington, DC
- August 3-5 – BSides Las Vegas
Where We've Been
- On February 19, Stephanie presented “No Water, No Hospitals, No Kidding” to the Louisiana Infragard chapter. Infragard, a group that partners with the Federal Bureau of Investigation and members of the private-sector for the protection of U.S. critical infrastructure, is an important venue to promote the U27 project to enhance both information sharing and education.
- On February 23, Josh and Stephanie presented on UnDisruptable27’s work at BSidesICS in Miami. While there, we met fellow ICS professionals; educated friends and new members of our network on U27’s important mission at the intersection of hospitals and water; and introduced Stephanie to a new community.
- On March 5-6, Josh and Stephanie attended a workshop in New Hampshire that was run by U27 volunteer and emergency doctor Malcolm Schongalla, MD. This Cyber-Resilient Health Care Workshop focused on innovation and implementation. While at Dartmouth, Josh ran a tabletop exercise focused on utilities and critical infrastructure and led a discussion with various medical professionals that provided valuable insight to enhance our efforts.
Our Media Diet
- On the heels of the new Trump National Cyber Strategy, Josh joined other IST experts in weighing in on March 6. He highlighted future opportunities for partnership in advancing the pillar on securing critical infrastructure: “When everything’s critical, nothing is. We’re most acutely concerned about threats to public safety and human life. UnDisruptable27 is eager to work with this White House and Executive Branch on ensuring ruthless prioritization for the fight that’s coming.”
- Josh’s remarks were featured in analysis and commentary in Politico and MeriTalk
- In a new report, operational technology firm Dragos said that Volt Typhoon remains embedded in U.S. utilities. In an interview with Recorded Future News, Dragos CEO Rob Lee said there are compromises in the United States and other NATO countries that “we will never find.”
- Last week, Josh spoke with CNN’s Sean Lyngaas on the pro-Iran regime attacks on the medical device manufacturer Stryker. “Too much of cybersecurity is focused on lower consequence breaches from financially motivated enemies, while we’re increasing our exposures to nation states and other enemies who seek to disrupt and destroy,” he told CNN. “China, Iran, Russia, etc. all have the means, motive, and opportunity to deal us devastating disruptions.”
- The Futureproofing Local Operations for Water Systems Act, introduced in Congress in March, could authorize $50 million annually for small and rural water utilities to modernize their cybersecurity protections and adopt digital monitoring tools, reports Sophia Fox-Sowell for Statescoop.
- New York Governor Kathy Hochul on March 11 announced $2.5 million available in grants for New York state communities to update their drinking water and wastewater solutions, along with minimum standards for mandatory cybersecurity training, incident reporting requirements, risk-based tiered standards, and designation of a cybersecurity lead at larger utilities.
Previous editions

Innovate narrowly, scale widely
From working with small and local communities to connecting with policymakers, UnDisruptable27’s mantra is to innovate narrowly and scale widely. As the team continues working to identify potential communities for piloting our cyber-informed, engineering first approach, we’re turning our attention to the policy sphere.

Save the Date for Critical Effect 2026
In the second issue of our newsletter, save the date for Critical Effect 2026, listen to the latest episode of Hack the Plan[e]t and other featured podcasts, and find out where to see us .

Happy Holidays from U27
In the inaugural edition of the UnDisruptable27 newsletter, learn how to participate in FrostyVolt’25, where to find us, and what we’ve been reading.





